- Hacker Tools Apk Download
- Hacker Tools 2020
- Growth Hacker Tools
- Hack Tools For Ubuntu
- Hacking Tools Kit
- Install Pentest Tools Ubuntu
- Pentest Tools Android
- Pentest Tools Bluekeep
- Hacker Tools 2019
- Pentest Tools For Windows
- Nsa Hacker Tools
- Pentest Tools Kali Linux
- Hacker Tools For Mac
- Bluetooth Hacking Tools Kali
- Pentest Tools For Ubuntu
- Pentest Tools Alternative
- Hack Tools For Windows
- Nsa Hack Tools
- Hacking Tools 2019
- Hacker Search Tools
- Pentest Tools Windows
- Hacking Tools And Software
- Free Pentest Tools For Windows
- Hak5 Tools
- Hack Tools
- Hak5 Tools
- Pentest Tools Framework
- Computer Hacker
- Hack Apps
- Hacking Tools Github
- How To Make Hacking Tools
- Top Pentest Tools
- Pentest Tools Free
- Hack Tools Online
- Easy Hack Tools
- Pentest Tools Find Subdomains
- Hacking Tools Hardware
- Hacker Security Tools
- Hack Tools For Windows
- Hacking Tools Software
- Hacking Tools Mac
- Blackhat Hacker Tools
- Hack Tools Github
- Pentest Tools Linux
- Physical Pentest Tools
- Hack Tools Pc
- Hacking Tools Mac
- Pentest Tools Port Scanner
- Hack Tools Github
- Pentest Tools Windows
- Hacking Tools Hardware
- Hacker Tools Online
- Hacker Tools For Mac
- Pentest Reporting Tools
- Hack Tools Online
- Hacking Tools Usb
- Pentest Tools Android
- Hacking Tools
- Pentest Tools Kali Linux
- Pentest Tools For Windows
- Hacking Tools And Software
- Hacker Tools Software
- Black Hat Hacker Tools
- Pentest Tools Tcp Port Scanner
- Pentest Tools Framework
- Hacking Tools Windows
- Pentest Tools List
- Hacker Tools 2019
- Hak5 Tools
- Underground Hacker Sites
- Hacking Tools Kit
- Easy Hack Tools
- Hacker Tools Software
- Hack Apps
- Hacking Tools
- New Hacker Tools
- Hacking Tools Windows
- Hacking Tools Usb
- Hacking Tools 2019
- Pentest Tools Review
- Hacker Tools Github
- Hacking Tools Name
- Hacker Tools Mac
- Pentest Tools Review
- Pentest Tools For Android
- Hacker Tools Apk
- Hacking Tools For Windows
- Hacker Tools Github
- Hack Tools For Windows
- Computer Hacker
- Hacking Tools For Games
- Hacking Tools For Windows Free Download
- Hackrf Tools
- Hack Tools For Windows
- Hacking Tools Online
- Hacker Tools Free Download
- Hack And Tools
- Hacking Tools For Kali Linux
- Hacking Tools Hardware
- Pentest Reporting Tools
- Android Hack Tools Github
- Hacking Tools For Mac
- Computer Hacker
- Hacks And Tools
- Hacking Tools For Kali Linux
- Hacker Tools 2020
- Best Hacking Tools 2020
- Hacking Tools 2019
- Hacking Tools Software
- Hack And Tools
- Pentest Recon Tools
- Hacking Tools And Software
- Black Hat Hacker Tools
- Black Hat Hacker Tools
- Android Hack Tools Github
- Hacking Tools Download
- Hacker Techniques Tools And Incident Handling
- Hak5 Tools
- Hack App
- How To Install Pentest Tools In Ubuntu
- Black Hat Hacker Tools
- Hacking Tools For Beginners
- Physical Pentest Tools
- Blackhat Hacker Tools
- Hack Website Online Tool
- Hacking Tools 2020
- Hack And Tools
- Hacker Security Tools
- New Hacker Tools
- Pentest Tools For Mac
- How To Hack
- Hack Tools For Ubuntu
- Hacking Tools For Windows 7
- Pentest Tools For Android
- Hacking Apps
- Pentest Tools
- Hacking Tools
- Hacking Apps
- Hacking Tools Mac
- Hacking Tools Windows
- Hacker Security Tools
- Pentest Tools For Windows
- Pentest Tools Android
- Hacker Tools Mac
- Hacker Tools Github
- Hacker Tools Free
- Hacking Tools Windows
- Pentest Tools Port Scanner
- Hacking Tools Free Download
- How To Hack
- Hacker Hardware Tools
- Hack Tools For Pc
- Hacking Tools For Games
- Hacking App
domingo, 28 de janeiro de 2024
Hackerhubb.blogspot.com
Vlang Binary Debugging
https://vlang.io/
After open the binary with radare in debug mode "-d" we proceed to do the binary recursive analysis with "aaaa" the more a's the more deep analys.
The function names are modified when the binary is crafted, if we have a function named hello in a module named main we will have the symbol main__hello, but we can locate them quicly thanks to radare's grep done with "~" token in this case applied to the "afl" command which lists all the symbols.
Being in debug mode we can use "d*" commands, for example "db" for breakpointing the function and then "dc" to start or continue execution.
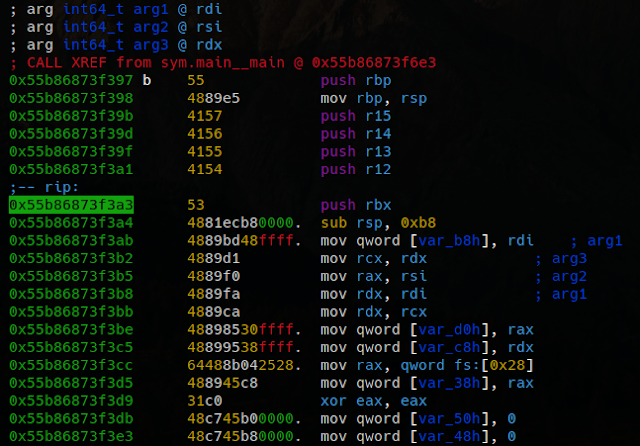
Let's dissasemble the function with "pD" command, it also displays the function variables and arguments as well, note also the xref "call xref from main"
Let's take a look to the function arguments, radare detect's this three 64bits registers used on the function.
Actually the function parameter is rsi that contains a testing html to test the href extraction algorithm.
The string structure is quite simple and it's plenty of implemented methods.
With F8 we can step over the code as we were in ollydbg on linux.
Note the rip marker sliding into the code.
We can recognize the aray creations, and the s.index_after() function used to find substrings since a specific position.
If we take a look de dissasembly we sill see quite a few calls to tos3() functions.
Those functions are involved in string initialization, and implements safety checks.
- tos(string, len)
- tos2(byteptr)
- tos3(charptr)
In this case I have a crash in my V code and I want to know what is crashing, just continue the execution with "dc" and see what poits the rip register.
In visual mode "V" we can see previous instructions to figure out the arguments and state.
We've located the crash on the substring operation which is something like "s2 := s1[a..b]" probably one of the arguments of the substring is out of bounds but luckily the V language has safety checks and is a controlled termination:
Switching the basic block view "space" we can see the execution flow, in this case we know the loops and branches because we have the code but this view also we can see the tos3 parameter "href=" which is useful to locate the position on the code.
When it reach the substr, we can see the parameters with "tab" command.
Looking the implementation the radare parameter calculation is quite exact.
Let's check the param values:
so the indexes are from 0x0e to 0x24 which are inside the buffer, lets continue to next iteration,
if we set a breakpoint and check every iteration, on latest iteration before the crash we have the values 0x2c to 0x70 with overflows the buffer and produces a controlled termination of the v compiled process.
Related news
- Hacking Tools And Software
- Pentest Tools For Mac
- Hackers Toolbox
- Hacking Tools For Windows
- Hack Tools Online
- Hacker Tool Kit
- Hackers Toolbox
- Hack Apps
- Hacking Tools 2019
- Pentest Tools Website
- Hacker Tools For Mac
- Pentest Tools Alternative
- Pentest Tools Find Subdomains
- World No 1 Hacker Software
- Pentest Tools Port Scanner
- Hack App
- Hacker Tools Apk
- Pentest Tools Url Fuzzer
- Hacking Tools For Beginners
- Pentest Tools Apk
- Hacker
- New Hacker Tools
- Nsa Hacker Tools
- Pentest Tools Windows
- Hacker Tools Github
- Hacking Tools For Kali Linux
- Hacking Tools Kit
- Physical Pentest Tools
- Pentest Tools Windows
- Hack Website Online Tool
- Hack Tools Mac
- Pentest Tools Website Vulnerability
- Hacker Tools Online
- Pentest Tools For Android
- Pentest Tools Bluekeep
- Wifi Hacker Tools For Windows
- Pentest Tools Alternative
- Hacker Tools For Ios
- Hacker Tools List
- Tools 4 Hack
- Pentest Tools Online
- Nsa Hack Tools
- Hackrf Tools
- Pentest Tools Windows
- Hacking Tools Kit
- Hacker Tools For Windows
- Pentest Box Tools Download
- Hacker Tools Free Download
- Hack Tools Mac
- Pentest Tools For Mac
- What Is Hacking Tools
- Hack Tools Online
- Hacking Tools Download
- Pentest Tools For Android
- Pentest Tools Kali Linux
- Hacking Tools Github
- Wifi Hacker Tools For Windows
- Hacking Tools 2019
- Hacking Tools 2019
- Hacker
- Game Hacking
- Pentest Tools For Mac
- Termux Hacking Tools 2019
- Hack Tool Apk
- Hacking Tools For Beginners
- Pentest Tools Port Scanner
- Hacker Tools Hardware
- Pentest Tools Bluekeep
- Hacker Tools
- Hacker Tools Free Download
- Hacker Tools Hardware
- Hacking Tools And Software
- Hacking Apps
- Hack Tools
- Pentest Tools Subdomain
- Hack Tools For Games
- Github Hacking Tools
- Hak5 Tools
- Pentest Tools
- Pentest Tools Url Fuzzer
- Bluetooth Hacking Tools Kali
- Pentest Tools Apk
- Pentest Tools Download
- Hacker Tools Linux
- Hacking Tools For Games
- Tools For Hacker
- Hack Website Online Tool
- Hacking Tools Pc
- Hacking Tools Free Download
- Pentest Tools For Ubuntu
- Hacking Tools For Mac
- How To Install Pentest Tools In Ubuntu
- Hacks And Tools
- Hack Tools Online
- Hack Tools Download
- Hacker Tools Github
- Hacker Search Tools
- Hacking Tools Hardware
- Hacker
- Nsa Hack Tools
- Nsa Hack Tools
- Hacker Tools Hardware
- Hak5 Tools
- Hacker Tools Free Download
- Pentest Tools Bluekeep
- Hacker Tools Free
- Pentest Tools Find Subdomains
- Pentest Tools For Mac
- Hacking Tools For Games
- Hack Tools For Pc
- Hacker Tools For Ios
- Hack Tools 2019
- Free Pentest Tools For Windows
- How To Hack
- Hacking Tools For Kali Linux
- Hacking Tools Hardware
- Hack Tools For Mac
- Pentest Tools For Android
- Pentest Tools Linux
- Hack Website Online Tool
- Hacks And Tools
- Hacking Tools And Software
- Hacker Tools Software
- Physical Pentest Tools
- Hacking Tools
- Hacker Tools
- Pentest Tools Github
- Hacker Tools Software
- Hack Apps
- Hacker Tools Linux
- Hacker Tools List
- Hacker Tools Free Download
- Hack Tools For Mac
- Hacking Tools And Software
- Hacking Tools For Kali Linux
- Hack Tools Github
- Hacker Tools Github
- What Is Hacking Tools
- Pentest Tools Find Subdomains
- Tools 4 Hack
- Install Pentest Tools Ubuntu
- Hack Tools For Games
- Hacker Tools For Mac
- Hacker Tools Linux
- New Hacker Tools
- Hacker Tools For Ios
- What Are Hacking Tools
- Blackhat Hacker Tools
- Pentest Automation Tools
- Hack Tools Github
- Hack Tools Mac
- How To Install Pentest Tools In Ubuntu
- Hacker Tools Hardware
- Kik Hack Tools
- Hacker Tools Hardware
- Pentest Tools For Ubuntu
- World No 1 Hacker Software
- Hacker Tools 2019
- Hacking Tools 2019
- Pentest Reporting Tools
- Hacker Techniques Tools And Incident Handling
- Hacker Tools 2019
- Hacking Tools 2020
- Hackers Toolbox
- Best Hacking Tools 2020
- Hacking Tools For Beginners
- Pentest Tools Github
- Pentest Tools Android
- Hak5 Tools
sábado, 27 de janeiro de 2024
DEFINATION OF HACKING
Hacking is an attempt to exploit a computer system vulnerabilities or a private network inside a computer to gain unauthorized acess.
Hacking is identifying and exploiting weakness in computer system and/ or computer networks for finding the vulnerability and loopholes.
Related news
- Hacking Tools Download
- Hack App
- Nsa Hack Tools Download
- Termux Hacking Tools 2019
- Pentest Tools Apk
- Hacker Search Tools
- Top Pentest Tools
- Nsa Hack Tools
- Hacker Tools Free Download
- Hacker Search Tools
- Pentest Tools Online
- Pentest Tools Linux
- Hacking Tools For Kali Linux
- Hack And Tools
- Pentest Tools Port Scanner
- Hacking Tools Name
- Github Hacking Tools
- Best Hacking Tools 2020
- Pentest Tools
- Hacker Hardware Tools
- Hacking Tools Free Download
- Hacker Tools For Mac
- Underground Hacker Sites
- Pentest Tools Github
- Hack Tool Apk
- Tools 4 Hack
- Wifi Hacker Tools For Windows
- Hacker Tools List
- Pentest Tools Kali Linux
- Hacking Tools For Pc
- Hack Tool Apk
- Hackrf Tools
- Hack Tools For Pc
- Hack Tool Apk
- Top Pentest Tools
- Hacker Tools Free
- Hackrf Tools
- Top Pentest Tools
- Bluetooth Hacking Tools Kali
- Hacking App
- What Are Hacking Tools
- Hacking Tools For Games
- Hack Tools Download
- Pentest Tools Download
- Best Pentesting Tools 2018
- Hack App
- Termux Hacking Tools 2019
- Pentest Recon Tools
- Hacker Tools Apk Download
- Hacking Tools And Software
- Beginner Hacker Tools
- Hackrf Tools
- Hacking Tools For Windows
- Hacking Tools 2019
- Physical Pentest Tools
- Hack Tool Apk No Root
- Pentest Tools Online
- Nsa Hacker Tools
- Hacker Tools List
- Hacker Tools
- Bluetooth Hacking Tools Kali
- Hacking Tools Software
- Hacker Tools Github
- Hacking Tools Pc
- Computer Hacker
- Pentest Tools Android
- Pentest Tools Linux
- Hacker Tools Mac
- New Hack Tools
- Hack Tools For Windows
- Kik Hack Tools
- Pentest Automation Tools
- Hack Tools
- Hacker Tools 2019
- Bluetooth Hacking Tools Kali
- Hacking Tools For Pc
- Pentest Tools Kali Linux
- Pentest Tools Framework
- Pentest Tools Url Fuzzer
- Hacker Tools Software
How SSPM Simplifies Your SOC2 SaaS Security Posture Audit
An accountant and a security expert walk into a bar… SOC2 is no joke.
Whether you're a publicly held or private company, you are probably considering going through a Service Organization Controls (SOC) audit. For publicly held companies, these reports are required by the Securities and Exchange Commission (SEC) and executed by a Certified Public Accountant (CPA). However, customers often ask for SOC2 reports as part of their vendor due diligence process.
Out of the three types of SOC reports, SOC2 is the standard to successfully pass regulatory requirements and signals high security and resilience within the organization — and is based on the American Institute of Certified Public Accountants (AICPA) attestation requirements. The purpose of this report is to evaluate an organization's information systems relevant to security, availability, processing integrity, confidentiality, and privacy — over a period of time (roughly six to twelve months).
As part of a SOC2 audit, it is necessary to conduct security checks across the company's SaaS stack that will look for misconfigured settings such as detection and monitoring to ensure continued effectiveness of information security controls and prevent unauthorized/ inappropriate access to physical and digital assets and locations.
If you're beginning or on a SOC2 audit journey, then an SSPM (SaaS Security Posture Management) solution can streamline the process and shorten the time it takes to pass a SOC2 audit successfully, fully covering your SaaS Security posture.
Learn how to streamline your organization's SOC2 compliance
What are the AICPA Trust Services Criteria (TSC)?
When external auditors engage in a SOC 2 audit, they need to compare what you're doing to a long list of established requirements from AICPA TSC. The "Common Controls" fall into five groups:
- Security - Includes sub controls of the Logical and Physical Access (CC6)
- Availability - Includes sub controls of the System Operations (CC7)
- Processing integrity: Includes sub controls of the System Operations (CC7)
- Confidentiality: Includes sub controls of the Logical and Physical Access (CC6)
- Privacy - Includes sub controls of the Monitoring Activities (CC4)
Within each common control are a set of sub controls that turn the overarching standard into actionable tasks.
Passing a SOC 2 audit takes a lot of time, effort, and documentation. During a SOC2 audit, you not only need to show that your controls work during the audit period, but you also need to show that you have the ability to continuously monitor your security.
Going through the entire TSC framework is too long for a blog post. However, a quick look into a couple of controls of Logical and Physical Access (CC6) and System Operations (CC7) gives you an idea of what some of the controls look like and how you can utilize an SSPM to ease the SOC2 audit.
Get a 15-minute demo of how an SSPM can help your SOC 2 TSC audit
Logical and Physical Access Controls
This section sets out the types of controls needed to prevent unauthorized or inappropriate access to physical and digital assets and locations. Managing user access permissions, authentication, and authorization across the SaaS estate poses many challenges. In fact, as you look to secure your cloud apps, the distributed nature of users and managing the different access policies becomes increasingly challenging.
Under CC6.1 control, entities need to:
- Identify, classify, and manage information assets
- Restrict & manage user access
- Consider network segmentation
- Register, authorize, and document new infrastructure
- Supplement security by encrypting data-at-rest
- Protect encryption keys
Example
The department that utilizes a SaaS app is often the one that purchases and implements it. Marketing might implement a SaaS solution for monitoring leads while sales implements the CRM. Meanwhile, each application has its own set of access capabilities and configurations. However, these SaaS owners may not be trained in security or able to continuously monitor the app's security settings so the security team loses visibility. At the same time, the security team may not know the inner workings of the SaaS like the owner so they may not understand more complex cases which could lead to a security breach.
An SSPM solution, maps out all the user permissions, encryption, certificates and all security configurations available for each SaaS app. In addition to the visibility, the SSPM solution helps correct any misconfiguration in these areas, taking into consideration each SaaS app's unique features and usability.
In CC.6.2 control, entities need to:
- Create asset access credentiations based on authorization from the system's asset owner or authorized custodian
- Establish processes for removing credential access when the user no longer requires access
- Periodically review access for unnecessary and inappropriate individuals with credentials
Example
Permission drifts occur when a user has certain permissions as part of a group membership, but then gets assigned a specific permission that is more privileged than what the group has. Over time many users get extra permissions. This undermines the idea of provisioning using groups.
Classic deprovisioning issues, an SSPM solution can spot inactive users and help organizations to quickly remediate, or at the very least, alert the security team to the issue.
Under CC.6.3 control, entities need to:
- Establish processes for creating, modifying or removing access to protected information and assets
- Use role-based access controls (RBAC)
- Periodically review access roles and access rules
Example
You might be managing 50,000 users across five SaaS applications, meaning the security team needs to manage a total of 250,000 identities. Meanwhile, each SaaS has a different way to define identities, view them, and secure identities. Adding to the risk, SaaS applications don't always integrate with each other which means users can find themselves with different privileges across different systems. This then leads to unnecessary privileges that can create a potential security risk.
An SSPM solution allows visibility into user privileges and sensitive permission across all connected SaaS apps, highlighting the deviation from permission groups and profiles.
System Operations
This section focuses on detection and monitoring to ensure continued effectiveness of information security controls across systems and networks, including SaaS apps. The diversity of SaaS apps and potential for misconfigurations makes meeting these requirements challenging.
In CC7.1 control, entities need to:
- Define configuration standards
- Monitor infrastructure and software for noncompliance with standards
- Establish change-detection mechanisms to aler personnel to unauthorized modification for critical system, configuration, or content files
- Establish procedures for detecting the introduction of known or unknown components
- Conduct periodic vulnerability scans to detect potential vulnerabilities or misconfigurations
It is unrealistic to expect from the security team to define a "configuration standard" that complies with SOC2 without comparing against a built-in knowledge base of all relevant SaaS misconfigurations and to continuously comply with SOC2 without using an SSPM solution.
Related articles- Hak5 Tools
- Hacker Tools Online
- New Hack Tools
- Hack Tools
- Hack Tool Apk No Root
- Pentest Tools Nmap
- Hacks And Tools
- How To Make Hacking Tools
- Hacking Tools 2019
- Hack And Tools
- Hak5 Tools
- Termux Hacking Tools 2019
- Hack Tools Github
- Hacker Tools Github
- Hack And Tools
- Hacker Tools Free Download
- Tools For Hacker
- Pentest Automation Tools
- Hacker Tools For Windows
- Kik Hack Tools
- Pentest Tools Subdomain
- Hacking Tools For Windows Free Download
- Pentest Tools Alternative
- Hacker Tools Github
- Best Hacking Tools 2020
- Pentest Recon Tools
- Pentest Box Tools Download
- Hacking Tools For Pc
- Hackrf Tools
- Hacker Tools Linux
- World No 1 Hacker Software
- Bluetooth Hacking Tools Kali
- Hacking Tools For Pc
- Best Hacking Tools 2019
- Hack Rom Tools
- New Hack Tools
- Hacks And Tools
- Computer Hacker
- Pentest Box Tools Download
- Hacker Tools Windows
- Tools Used For Hacking
- Pentest Tools Subdomain
- Pentest Tools Find Subdomains
- Pentest Tools For Ubuntu
- Hacker Tools Windows
- Pentest Tools Linux
- Physical Pentest Tools
- Hacking Tools For Games
- Hacking Tools For Pc
- Hacking Tools
- Pentest Tools For Android
- Hack Tools For Pc
- Pentest Tools Subdomain
- Hacker Tools Apk
- Pentest Tools List
- Hacker Tools List
- Hack Tools
- Best Hacking Tools 2020
- Hacker Tools For Mac
- Hacking Tools For Kali Linux
- Hak5 Tools
- Hacking Tools Pc
- Pentest Recon Tools
- Hack Tools
- Hacker Tools Linux
- Hacker Tools List
- Pentest Tools Review
- Hack Rom Tools
- Hacking Tools Mac
- Hacker Tools 2020